Entrust IdentityGuard is carried or worn around the neck of the individual. Image Credit: Entrust, Inc. via Avisian publications
Entrust IdentityGuard is carried or worn around the neck of the individual. Image Credit: Entrust, Inc. via Avisian publicationsBest ID Security May Not Be Just Biometric
Specific identification of an individual short of a DNA make-up can be achieved through many identification processes. A large investment has been made in systems based on biometric access, radio based proximity information exchange, and video software that can recognize individuals through data mining identifiers associated with ones face ... or body type.
Maybe the best identification solution to implement can also be one of the simplest. Maybe the easiest way to insure the identification of an individual is to rely on a two step authentication process that requires the individual, after entering a password, to interact with the process via a matrix matching grid that uses the individual's brain.
Oh, and by the way, this security solution is inexpensive and simple to implement.
Excerpts from CR80News -
Grid-based two-factor authentication comes to campus cards
Sweden’s Goteborg University deploys a visual challenge and response solution from Entrust
By Andy Williams, Contributing Editor, CR80News - Monday, September 25 2006
You log in with your password, then you're met with another screen with the following: A3, F4, J5. No, you're not playing Bingo. It's part of an authentication system created by Dallas, Texas-based Entrust. To supply the correct answers to A3, F4 and J5, you need a grid supplied by the company. It's a security solution that one Swedish university has chosen to protect its student records.
 Entrust IdentityGuard "X-Y" matrix grid pad. Image Credit: Entrust, Inc. via Avisian publications
Entrust IdentityGuard "X-Y" matrix grid pad. Image Credit: Entrust, Inc. via Avisian publications"Grid authentication is about an X-Y coordinate lookup system," said Steve Neville, senior manager of ID products and solutions for Entrust, Inc. a secure digital identity provider. "It's like reading a map and it's about being able to respond to the random challenges of a coordinate on a grid."
To help prevent attacks on student data and protect the records of its 60,000 students and faculty while facilitating access for authorized parties, Goteborg University in Sweden recently implemented Entrust's IdentityGuard.
----
A cost-conscious option for multi-factor authentication
The two-factor authentication system requires a password, plus the grid that's often printed on the back of a student's or faculty member's identification card, said Mr. Neville. It's a standard student card that's usable not only for identification but for other things, like accessing foodservice.
----
Either way, the grid is useless without the password and the password useless without the grid. The grid is the 'something you have' and the password is the 'something you know' in the multi-factor authentication scenario.
----
"We wanted an authentication solution that would provide strong security but also would be easy to use for our students and faculty and also be economical to manage," said Sven-Elof Kristenson, IT manager at Goteborg University. "Because we can combine the Entrust IdentityGuard grid authentication capability with the identity cards we already issue to our students and faculty at the beginning of the school term, it fit seamlessly into our existing system and will give us the ability to make even more services available online for everyone."
The university also chose IdentityGuard because its grid authentication capability can be used to access records, file storage, reports, e-mail and calendar functions, said Mr. Neville. "It was a natural choice for stronger authentication. Ease of integration and usability also were factors that led to the decision to implement Entrust IdentityGuard."
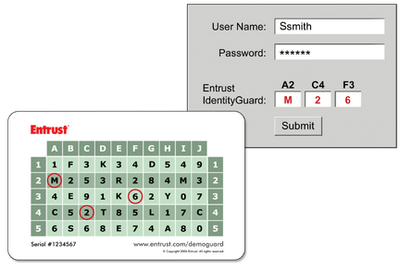 Entrust IdentityGuard matrix grid pad information as it is applied to a computer log-in screen. Image Credit: Entrust, Inc. via Avisian publications
Entrust IdentityGuard matrix grid pad information as it is applied to a computer log-in screen. Image Credit: Entrust, Inc. via Avisian publicationsAdding 'machine fingerprinting' to the grid authentication
"ID Guard in and of itself is a platform for authentication," said Mr. Neville. It comes in six different flavors-authentication options --- ranging from the non-intrusive like machine fingerprinting and grid authentication to one-time password tokens, he added.
"One of the reasons Goteborg liked grid authentication is that it also delivers the flexibility to input other types of authentication. Inside our license model we don't force them to track which authentication they're using. They can choose which ones they want to use to protect student data," said Mr. Neville.
A risk can be assigned to student data to determine the type of authentication needed, he added. "It can be a simple process, like this type of information requires the grid and machine authentication. For students, the grid is totally fine because they're roaming around," said Mr. Neville.
ID Guard is a "software server based product that can also provide strong authentication for remote access," he added.
----
"When they (Goteborg University officials) were looking at security solutions, they were very sensitive to cost and how much change would be required. They looked at ID Guard as a very attractive solution versus one that could only be deployed to faculty alone because of the cost. It was also something they found very unique and something they could trust."
Read All>>