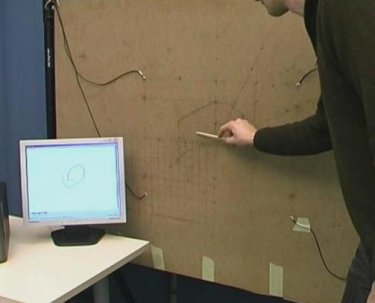
When an unsuspecting reader scans an infected tag, there is a danger of the tag exploiting vulnerability in the middleware to cause unwanted actions to occur, which may include infecting the database. This is a photo of the world's first RFID tag identified with a virus. Image Credit: Department of Computer Science, Vrije Universiteit Amsterdam
When an unsuspecting reader scans an infected tag, there is a danger of the tag exploiting vulnerability in the middleware to cause unwanted actions to occur, which may include infecting the database. This is a photo of the world's first RFID tag identified with a virus. Image Credit: Department of Computer Science, Vrije Universiteit Amsterdam
"Sick" RFID tags - A Real Threat To Systems
Many who work with RFID systems falsely believe that the only threat of virus infection to the computer's programs is through the standard entry points (new program downloads and transference, emails, hackers, and etc.).
A new entry point has been found and at this point, there are no ironclad defenses to this simple act of just "scanning a tag".
Excerpts from the Department of Computer Science, Vrije Universiteit Amsterdam -
RFID Viruses and Worms
By Melanie R. Rieback, Patrick N. D. Simpson, Bruno Crispo, Andrew S. Tanenbaum - Department of Computer Science, Vrije Universiteit Amsterdam
Unfortunately, businesses and governments are not the only ones interested in RFID. Civil liberties groups, hackers and criminals are also keenly interested in this new development, albeit for very different reasons. Civil liberties groups are concerned about RFID technology being used to invade people's privacy; RFID tags enable unethical individuals to snoop on people and surreptitiously collect data on them without their approval or even knowledge. For example, RFID-enabled public transit tickets could allow public transit managers to compile a dossier listing all of a person's travels in the past year -- information which may be of interest to the police, divorce lawyers, and others.
However, privacy is not the focus of this website and will not be discussed further below. On the other hand, we are intensely concerned about privacy in an RFID-enabled world and have built an entire sister website about a device we have constructed, called the RFID Guardian, which could potentially help people protect their privacy from RFID snooping in the future. Those interested in RFID and privacy might want to check it out at www.rfidguardian.org. The website even includes a video of the prototype RFID Guardian in action.
A completely different category of threats arises when hackers or criminals cause valid RFID tags to behave in unexpected (and generally malicious) ways. Typically, computer-bound or mobile RFID readers query RFID tags for their unique identifier or on-tag data, which often serves as a database key or launches some real-world activity. For example, when an RFID reader at a supermarket checkout counter reads the tag on a product, the software driving it could add the item scanned to the list of the customer's purchases, tallying up the total after all products have been scanned.
Here is where the trouble comes in. Up until now, everyone working on RFID technology has tacitly assumed that the mere act of scanning an RFID tag cannot modify back-end software, and certainly not in a malicious way. Unfortunately, they are wrong. In our research, we have discovered that if certain vulnerabilities exist in the RFID software, an RFID tag can be (intentionally) infected with a virus and this virus can infect the backend database used by the RFID software. From there it can be easily spread to other RFID tags. No one thought this possible until now.
----
While we have some hesitation in giving the "bad guys" precise information on how to infect RFID tags, it has been our experience that when talking to people in charge of RFID systems, they often dismiss security concerns as academic, unrealistic, and unworthy of spending any money on countering, as these threats are merely "theoretical." By making code for RFID "malware" publicly available, we hope to convince them that the problem is serious and had better be dealt with, and fast. It is a lot better to lock the barn door while the prize race horse is still inside than to deal with the consequences of not doing so afterwards.
Real-World Scenarios
To make clear what kinds of problems might arise from RFID hacking by amateurs or criminals, let us consider three possible and all-too-realistic scenarios.
I.) A prankster goes to a supermarket that scans the purchases in its customers' shopping carts using the RFID chips affixed to the products instead of their bar codes. Many supermarkets have plans in this direction because RFID scans are faster (and in some cases can be done by the customers, eliminating the expense of having cashiers). The prankster selects, scans, and pays for a nice jar of chunk-style peanut butter that has an RFID tag attached to it. Upon getting it home, he removes or destroys the RFID tag. Then he takes a blank RFID tag he has purchased and writes a exploit on it using his home computer and commercially available equipment for writing RFID tags. He then attaches the infected tag to the jar of peanut butter, brings it back to the supermarket, heads directly for the checkout counter, and pays for it again. Unfortunately, this time when the jar is scanned, the virus on its tag infects the supermarket's product database, potentially wreaking all kinds of havoc such as changing prices.
II.) Emboldened by his success at the supermarket, the prankster decides to unwittingly enlist his cat in the fun. The cat has a subdermal pet ID tag, which the attacker rewrites with a virus using commercially available equipment. He then goes to a veterinarian (or the ASPCA), claims it is stray cat and asks for a cat scan. Bingo! The database is infected. Since the vet (or ASPCA) uses this database when creating tags for newly-tagged animals, these new tags can also be infected. When they are later scanned for whatever reason, that database is infected, and so on. Unlike a biological virus, which jumps from animal to animal, an RFID virus spread this way jumps from animal to database to animal. The same transmission mechanism that applies to pets also applies to RFID-tagged livestock.
III.) Now we get to the scary part. Some airports are planning to expedite baggage handling by attaching RFID-augmented labels to the suitcases as they are checked in. This makes the labels easier to read at greater distances than the current bar-coded baggage labels. Now consider a malicious traveler who attaches a tiny RFID tag, pre-initialized with a virus, to a random person's suitcase before he checks it in. When the baggage-handling system's RFID reader scans the suitcase at a Y-junction in the conveyor-belt system to determine where to route it, the tag responds with the RFID virus, which could infect the airport's baggage database. Then, all RFID tags produced as new passengers check in later in the day may also be infected. If any of these infected bags transit a hub, they will be rescanned there, thus infecting a different airport. Within a day, hundreds of airport databases all over the world could be infected. Merely infecting other tags is the most benign case. An RFID virus could also carry a payload that did other damage to the database, for example, helping drug smugglers or terrorists hide their baggage from airline and government officials, or intentionally sending baggage destined for Alaska to Argentina to create chaos (e.g., as revenge for a recently fired airline employee).
Some companies with a vested interest in RFID technology have said their software can withstand attacks such as the ones we have proposed. We hope that is the case. These claims would be much more believable, however, if the companies made their software available to universities and other neutral parties for exhaustive testing, along with a large reward (say, $100,000) for the first person to construct a virus that successfully infects it. If no one is able to infect the software after, say 6 months, the claim that the software cannot be infected is a great deal stronger than merely stating it without proof. The nice part of this for the company is that if the software is bulletproof, it costs the company nothing.
Reference Here>>
STOP sneezy, drippy, virus laden tags now!
Suggested research links (the links give more technical detail about possible attacks and how to prevent them) - best viewed in order of listing:
RFID Middleware
Classes of RFID Malware
The Architecture of RFID Systems
Vulnerabilities that Can Be Exploited
How to Write an RFID Virus
How to Write an RFID Worm
How to Defend against RFID Malware

 A QR Code printed 36 feet by 36 feet on a banner and hung on the side of a building in Hiroshima, Japan. Image Credit: PlusD Mobil/IT Media, Inc.
A QR Code printed 36 feet by 36 feet on a banner and hung on the side of a building in Hiroshima, Japan. Image Credit: PlusD Mobil/IT Media, Inc.